Blog Articles
The Real Deal
The content below is real, authored by us. We do not use syndicated content nor do we outsource the authoring to some marketing firm or AI (though we do have AI help us do editing). When you read the blogs below, you are hearing from real, live, people at JNR.
Core Utility of IT – IT Hierarchy Part 2
Welcome to part 2 of our 5 part series! In our last blog, we explored Maslow’s Hierarchy of Needs and it’s connection to IT. This week, we delve into the first of four layers in our model: the Core Utility of IT.
Maslow’s Hierarchy of Needs and IT’s Hierarchy
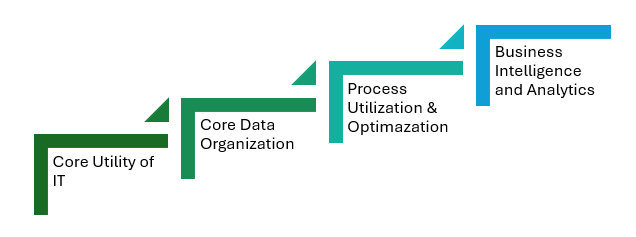
I have been “doing” IT for over 30 years, and throughout this journey, I have often felt that the typical IT conversation—centered solely on “making the systems work”—is incomplete. While it is undeniably important for our systems to function properly so we can get our work done, this approach doesn’t capture the full potential of IT. It is like focusing only on the foundation of a building without considering the structure and design that make it truly functional and beautiful.
It’s About Customer Service!

In recent weeks, I’ve encountered both dismal and outstanding examples of customer service. While companies invest heavily in marketing to attract new clients, they often neglect their existing ones. It’s surprising how frequently basic customer service is overlooked, despite its significant benefits.
What is the Deal with Remote Offices?

Over the years, I’ve been honored to be present at a annual conference in Orlando on how we’ve successfully built our business and culture with a 100% remote workforce. Technological advancements have made it possible for people to work remotely with access to IT resources comparable to those available onsite. However, thriving in a remote environment requires paradigm shifts and maturity from both the team members and leadership.
Data and the Expectation of Privacy
As technology rapidly advances, it’s easy to get swept up in the excitement of new possibilities. The rise of cloud computing, in particular, has opened up numerous opportunities. However, with this increased capacity, it’s crucial to ask, “Just because we can, does that mean we should?”
Navigating the Challenges of Hiring in the IT Industry

Over the years, our journey to find and hire exceptional talent has been fraught with challenges. Initially, our struggle stemmed from a lack of clarity about our needs and the discipline to adhere to them. Now that we have a solid understanding of the qualities that make someone a good fit for our team, a new challenge has emerged: finding those individuals.
Building a Culture of Continuous Improvement

In a previous blog, we discussed how to write effective Standard Operating Procedures (SOPs). While this is a crucial step, it’s only the beginning. For businesses, people, and processes to thrive, continuous improvement is essential. The challenge lies in making this a consistent practice.
Nervous vs Excited

Earlier this year, in a blog titled “Here’s to the Crazy Ones”, I discussed our approach to failure and our attitude towards it. There is an insightful video from Simon Sinek, along the vein of thinking, about training your mind to perform under pressure, and I wanted to share it with you.
Key Insights to Writing Great SOPs

Over the years, I have had the privilege of speaking at one of the premier IT industry events in Orlando, FL at least once a year. One of the sessions I presented was titled “SOPs for your SOPs,” which covered two essential topics: how to write great Standard Operating Procedures (SOPs) and how to build a solid culture around continual process improvement. While I tend to focus heavily on identifying our flaws and continuously seeking improvement, I sometimes overlook the importance of recognizing what we do well. It was both rewarding and an honor to share with the attendees what we have learned, often from our own mistakes. In this blog, I’m going to focus on the critical elements we have found necessary for writing great SOPs.
The Spirit vs the Letter of the Law in Handbook Policies
When helping clients draft IT policies for their Employee Handbooks, I often find myself torn between two approaches. One part of me wants to detail every aspect of the policies, while another part wants to simply say, “Do the right thing!” This tension highlights the different methods of policy writing: one that specifies every detail and another that provides a broad vision of right and wrong, leaving room for common sense.
Tags
Let’s Connect
We would love to hear from you. If you have questions about how we may be able to work together, click the button below, fill out the form and we will connect to explore the future together.
